PSA: Lemmy.world has been compromised! (Edit: Multiple Instances are down) (lemmy.ml)
cross-posted from: https://lemmy.ml/post/1895271...
This magazine is from a federated server and may be incomplete. Browse more on the original instance.
cross-posted from: https://lemmy.ml/post/1895271...
Researchers say that nearly 336,000 devices exposed to the Internet remain vulnerable to a critical vulnerability in firewalls sold by Fortinet because admins have yet to install patches the company released three weeks ago....


Unidentified hackers claimed to have targeted Dozor, a satellite telecommunications provider that services power lines, oil fields, Russian military units and the Federal Security Service (FSB), among others, according to a message posted to Telegram late Wednesday night....

The Russian-linked hacktivist group NoName has been relentlessly targeting the Ukrainian financial sector in its latest campaign against the war-torn nation....
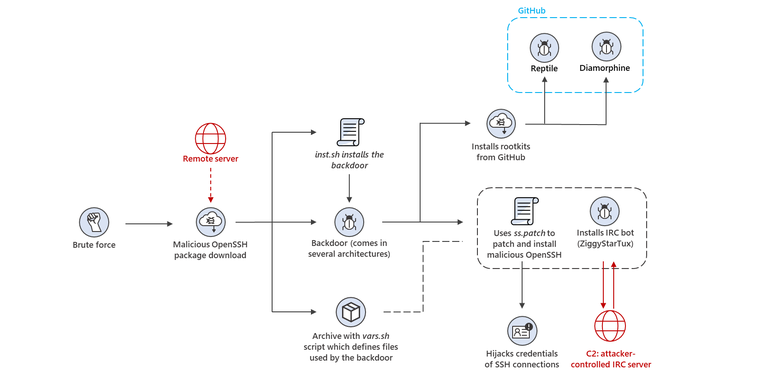
Microsoft researchers have recently discovered an attack leveraging custom and open-source tools to target internet-facing Linux-based systems and IoT devices. The attack uses a patched version of OpenSSH to take control of impacted devices and install cryptomining malware....
SolarWinds — the technology firm at the center of a December 2020 hack that affected multiple U.S. government agencies — said its executives may soon face charges from the U.S. Securities and Exchange Commission (SEC) for its response to the incident....

A year after the Russian invasion of Ukraine, MITRE efforts to develop and deliver needed technology and relief endure, and grow, helping the people on the ground who need it most ....
Microsoft has disclosed that it's detected a spike in credential-stealing attacks conducted by the Russian state-affiliated hacker group known as Midnight Blizzard....

BlackLotus is a sophisticated piece of malware that can infect a computer's low-level firmware, bypassing the Secure Boot defences built into Windows 10 and Windows 11, and allowing the execution of malicious code before a PC's operating system and security defences have loaded....

Apple issued a security update on Wednesday for all its operating systems to patch dangerous vulnerabilities that could allow attackers to take over someone’s entire device....

I'm a newbie to podcasts, but I got hooked recently because I can listen while doing something else....
TIL the French government may have broken encryption on a LUKS-encrypted laptop with a "greater than 20 character" password in April 2023....
Executive summary...

Cybercrime has become a dominant concern for many businesses, as well as individuals. Cybercriminals will target any business, and any individual if they can realize a profit from their minimal efforts. One of the ways that criminals achieve their goals is through the use of malware that garners a fast profit, such as...

The U.S. Army’s Criminal Investigation Division is urging military personnel to be on the lookout for unsolicited, suspicious smartwatches in the mail, warning that the devices could be rigged with malware....

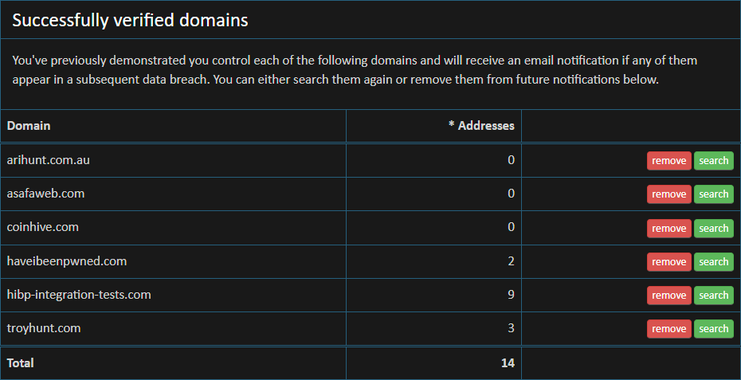
There are presently 201k people monitoring domains in Have I Been Pwned (HIBP). That's massive! That's 201k people that have searched for a domain, left their email address for future notifications when the domain appears in a new breach and successfully verified that they control the domain. But that's only a subset of all the...
A new policy directive from Maine Information Technology (MaineIT) has put a six-month moratorium on the adoption and use of Generative Artificial Intelligence (AI) technology within all State of Maine agencies due to “significant” cybersecurity risks....

The BBC CISO says she is a “consummate cynic” about cybersecurity certifications. Helen Rabe believes schemes like the widely recognised ISO 27001 standard are “time consuming” and “cumbersome” to maintain for tech teams, and could be ripe for reform....

Every cybersecurity vendor has a different vision of how generative AI will serve its customers, yet they all share a common direction. Generative AI brings a new focus on data accuracy, precision and real-time insights. DevOps, product engineering and product management are delivering new generative AI-based products in record...

cross-posted from: https://kbin.social/m/tech/t/67505...

Complex, well-resourced, and well-organized, Anonymous Sudan looks like a front group for an intelligence service....

Tesla CEO Elon Musk might have his very own supersecret driver mode that enables hands-free driving in Tesla vehicles....

Cybersecurity provider Trend Micro Incorporated has been integrating artificial intelligence (AI) into its technologies for a decade, but it hasn’t had the power of generative AI, until now....

From the moment I began my freelance web design business back in 2014, I was collecting payments via Stripe and happily paying their processing fees for the ability to grow my business from just a desire for more freedom to running a company that employs women and supports them to create their own freedom and financial...
