[tl;dr sec] #215 - Cloud Threat Landscape, Web LLM Security Labs, Azure Logs Primer (tldrsec.com)

This magazine is from a federated server and may be incomplete. Browse more on the original instance.






cross-posted from: infosec.pub/post/5707149...


This is my first write-up, on a vulnerability I discovered in iTerm2 (RCE). Would love to hear opinions on this. I tried to make the writing engaging.
Mobile Application Security Cheat Sheet...







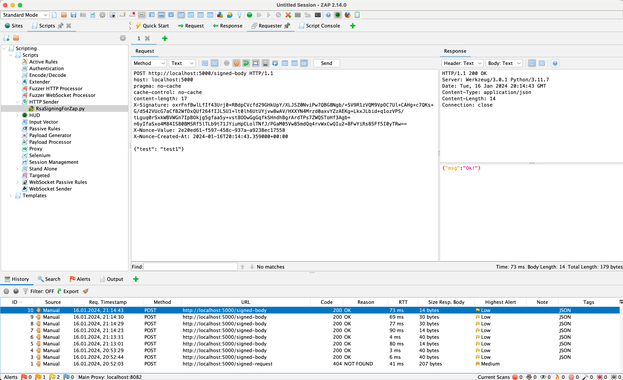
You might have found HTML injection, but unfortunately identified that the site is protected with CSP. All is not lost, it might be possible to bypass CSP using DOM clobbering, which you can now detect using DOM Invader! In this post we’ll show you how....

