Secure Operating Systems (Microkernels seems to be the future)
I am not satisfied with Linux’s security and have been researching alternative open source OS for privacy and security So far only thing that’s ready to use is GrapheneOS (Based on Android) but that’s not available on desktop (Though when Android release Desktop mode it may become viable)
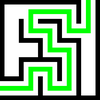
Qubes OS is wrapper around underlying operating systems, so it doesn’t really fix for example Linux’s security holes it just kinda sandbox/virtualize them
OpenBSD is more secure than Linux on a base level but lack mitigations and patches that are added to linux overtime and it’s security practices while good for it’s time is outdated now
RedoxOS (Written in Rust) got some nice ideas but sticks to same outdated practices and doesn’t break the wheel too much, and security doesn’t seems to be main focus of OS
Haiku and Serenity are outright worse than Linux, especially Haiku as it’s single user only
Serenity adopted Pledge and Unveil from OpenBSD but otherwise lacks basic security features
All new security paradigms seems to be happening in microkernels and these are the ones that caught my eyes
None of these are ready to be used as daily driver OS but in future (hopefully) it may change
Genode seems to be far ahead of game than everything else
Ironclad Written in ADA
Atmosphere And Mesosphere Open Source Re-implementation of Nintendo Switch’s Horizon OS, I didn’t expected this to be security-oriented but seems like Nintendo has done a very solid job
Then there are Managarm, HelenOS, Theseus but I couldn’t figure out how secure they are
Finally there is Kicksecure from creators of Whonix, Kicksecure is a linux distro that plans to fix Linux’s security problems
if you know of any other OS please share it here



Add comment